Sometimes there is no authoritative source. Sometimes you just have to say, "Bob, provision me a user." These are the cases where you will need a very flexible user interface to control user provisioning workflows.
 See, that's the cool part, the UI is just what initiates the workflows in EmpowerID, the exact same workflows that are used when it detects a new employee in the HR system. The same series of events are kicked off: assignment of roles, membership in groups, new accounts in the cloud, notification to the party planning committee, a single sign on dashboard. It's all there, you are just starting it differently.
See, that's the cool part, the UI is just what initiates the workflows in EmpowerID, the exact same workflows that are used when it detects a new employee in the HR system. The same series of events are kicked off: assignment of roles, membership in groups, new accounts in the cloud, notification to the party planning committee, a single sign on dashboard. It's all there, you are just starting it differently.
Of course, authoritative sources are called that because they have authority. You can trust them. With delegated user provisioning, you need to have some additional controls. The simplest and most efficient is to have an approval workflow shape where somebody in authority has to approve the new user. Or approve any role with a security level over XYZ. These approvals can be serial or parallel, they can go to someone in IT or HR or anywhere in between. They can be decided based on who the new user is. The important part is that one rogue employee won't be creating any domain admins named Joe Derp.
Another consideration is the complexity of the user interface. EmpowerID ships with over 400 usable out of the box identity management workflow templates. About ten of these include user provisioning forms, ranging from what we call "super simple user provisioning" to "user provisioning".
The difference is what fields are required. In super simple, the user puts in the name, department, title, and location of the user and EmpowerID dynamically assigns roles. In simple, there is a dropdown of available roles depending on the attributes already defined and who the requester is (help desk can create X roles and HR can create Y roles for example). There is also an IT based form where a sys admin who understands things like OU structures and the such can granularly define any attribute.
Just my own personal opinion is that delegated user provisioning should always have an initial lifecycle. This is easily accomplished by adding an expiration date dropdown on the form or creating a business rule in the workflow that it needs to be certified and renewed within that date period to continue its existence. This is basically adding attestation to any user provisioning that happens outside of automated processes.
The reason I believe this attestation and lifecycle are important is the use cases for delegated user provisioning. The most obvious ones are:
- temporary employees or contractors
- task based highly privileged accounts
- additional accounts for an existing user
- partners and suppliers accounts
None of these types of accounts should be subject to having perpetual access and permissions within your network. With a strong IAM platform like EmpowerID, these security concerns can be alleviated even on users provisioned outside of normal channels.
Take a look at this video demonstrating EmpowerID's role-based user provisioning; you can see some examples of the delegated user provisioning forms (because showing automated user provisioning makes for a boring demo :) ). Then schedule a personalized demonstration where we can help you start designing your own user provisioning processes.

 EmpowerID believes in the philosophy that teaching a man to fish will keep him fed for a lifetime. The same thing applies with identity management, it should not be a software that you need to keep hiring consultants every time you want to make a change to your business processes.
EmpowerID believes in the philosophy that teaching a man to fish will keep him fed for a lifetime. The same thing applies with identity management, it should not be a software that you need to keep hiring consultants every time you want to make a change to your business processes.
 The real trick is what you allow them to update via self service. Most shops allow some limited Active Directory self service. But there is so much more that you can open up with a well designed self service identity management system...as long as you put controls, approvals and lifecycle into effect.
The real trick is what you allow them to update via self service. Most shops allow some limited Active Directory self service. But there is so much more that you can open up with a well designed self service identity management system...as long as you put controls, approvals and lifecycle into effect.
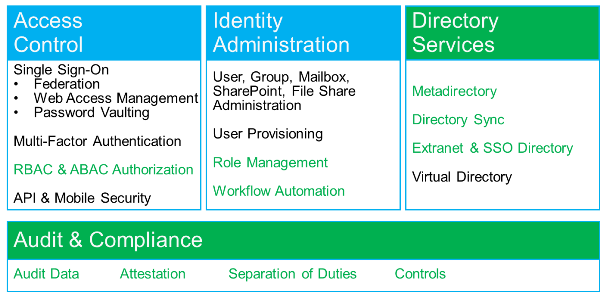
 Lifecycle exists everywhere, but very specifically in identity management. The "phrase du jour" appears to be Identity Governance and Administration but at one point it was Identity Lifecycle Management...lifecycle is the governance and administration part of the new phrase.
Lifecycle exists everywhere, but very specifically in identity management. The "phrase du jour" appears to be Identity Governance and Administration but at one point it was Identity Lifecycle Management...lifecycle is the governance and administration part of the new phrase.
 The OATH encryption algorithm is an open source standard and, as such, is widely available. EmpowerID ships with an OATH server to encrypt the OATH token while clients such as Google Authenticator are free and widely available for smart phones and tablets.
The OATH encryption algorithm is an open source standard and, as such, is widely available. EmpowerID ships with an OATH server to encrypt the OATH token while clients such as Google Authenticator are free and widely available for smart phones and tablets.
 In a perfect world, all of your applications would run on one OS, built by one vendor and speak to each other seamlessly. Every user of every application would have the correct level of access and sign on easily with a single set of secure credentials. Of course, this perfect world doesn't exist and will never exist.
In a perfect world, all of your applications would run on one OS, built by one vendor and speak to each other seamlessly. Every user of every application would have the correct level of access and sign on easily with a single set of secure credentials. Of course, this perfect world doesn't exist and will never exist.
 Where we always do better than our competition is our IAM implementation plan. We believe in putting the full solution and plan and cost and SOW up front to help make the decision easier for our clients. Other vendors don't always do that; if you found this blog post by searching for IAM implementation plan then you might already realize that. Here are the items to consider when looking for an implementation plan from your IAM vendor.
Where we always do better than our competition is our IAM implementation plan. We believe in putting the full solution and plan and cost and SOW up front to help make the decision easier for our clients. Other vendors don't always do that; if you found this blog post by searching for IAM implementation plan then you might already realize that. Here are the items to consider when looking for an implementation plan from your IAM vendor.
 Remember your first day on the job at your company, you were given access to a few things, keys to the kingdom if you will. A year later you were promoted, given new responsibilities and a few more of these "keys". By the time you've been at a company for a few years, your "keychain" looks like one of those giant keyrings that a NY super has.
Remember your first day on the job at your company, you were given access to a few things, keys to the kingdom if you will. A year later you were promoted, given new responsibilities and a few more of these "keys". By the time you've been at a company for a few years, your "keychain" looks like one of those giant keyrings that a NY super has.
 This problem is exacerbated due to SAP HCM's e-recruitment capabilities and the need to create accounts and identities for job applicants. They can't be expected to wait for such a long time to have access to systems that they need for their job application.
This problem is exacerbated due to SAP HCM's e-recruitment capabilities and the need to create accounts and identities for job applicants. They can't be expected to wait for such a long time to have access to systems that they need for their job application.