Organizations that manage successful brands know what their customers want from a website experience and are able to provide it.
Consumers want simpler processes.
They want a quick, seamless authentication experience.
They want to get to a site from any device that is handy at the time, whether it’s a pc, a tablet or a smartphone.
They have lots of choices and they are bombarded with lots of information. Your branding must be visible and the flow of your customer through your site must be smooth so they will have a positive experience, remember you and want to return.
And your security for their identity needs to protect them and you without being obtrusive.
Your prize, if you capture consumers with a well-designed web presence, is a solid foundation for business growth, faster fulfilment of your clients’ needs, and substantially greater efficiencies that can reduce costs and drive profitability.
And of course you are supposed to accommodate all that and keep to a modest IT budget… phew!
Here’s what it’s going to take:
- A highly scalable Single Sign On (SSO) and Identity and Access Management (IAM) platform – one that can take you where your ambition wants to go. Your IAM infrastructure may need to manage millions of users and tens of thousands of logins an hour.
- Flexible branding – the login process can’t be generic, it and related Single Sign On (SSO) pages need to be customizable to your themes.
- Support for social media logins is a must if you want to simplify the user experience and entice the widest number of users possible.
- Self-service password reset and challenge questions that allows consumers to quickly get back in to your site if they forget their username or their password.
- 2nd factor authentication capabilities and even identity validation will be needed if you need to provide an extra level of protection for your data or resources. You may want the ability to step up authorization when a user needs to access more sensitive information.
- A flexible API is another core need – on that can be embedded into your existing applications to connect to common authentication, provisioning and authorization processes.
- You will want a licensing model that scales from a modest user base to one that is still affordable if you exceed your best expectations.
- And while many SSO platforms claim that you can easily entrust provisioning to another platform that they can connect to, that’s going to cost you more money to develop, to implement and to support. So you will want a platform that is capable of integrating all of your essential identity management tasks from the start.
- There is a lot of other technical stuff that you are going to want, like compatibility with all the major standards (SAML, WS-Fed, OAuth), password vaulting and reverse proxy for those legacy apps that can’t make a standard federated connection, but that still need to talk to your federated environment (because throwing out everything you own to pave way for new standards isn’t always practical).
There is a solution that provides all of the above: EmpowerID.
EmpowerID is an integrated and modular platform, built on a single codebase and driven by workflow with prebuilt one-to-many SSO and Identity Management scenarios with the needs of consumers in mind.
EmpowerID’s visual workflow designer and adaptive HTML5 interfaces offer a vastly improved and simplified approach to traditional SSO and IAM challenges. It can be stood up in just a few days or weeks depending on the customization desired, instead of the months that other applications take.
Most importantly, EmpowerID supports a satisfying access experience for consumers and drives strong ROI with its secure, seamless and flexible identity processes.



 The OATH encryption algorithm is an open source standard and, as such, is widely available. EmpowerID ships with an OATH server to encrypt the OATH token while clients such as Google Authenticator are free and widely available for smart phones and tablets.
The OATH encryption algorithm is an open source standard and, as such, is widely available. EmpowerID ships with an OATH server to encrypt the OATH token while clients such as Google Authenticator are free and widely available for smart phones and tablets.
 Active Directory password management is a three part problem: self service password reset; password synchronization to other applications; and to eliminate passwords entirely!!!!
Active Directory password management is a three part problem: self service password reset; password synchronization to other applications; and to eliminate passwords entirely!!!!
 Just don't stop at Active Directory. There are more passwords out there, a lot more. A study of just
Just don't stop at Active Directory. There are more passwords out there, a lot more. A study of just 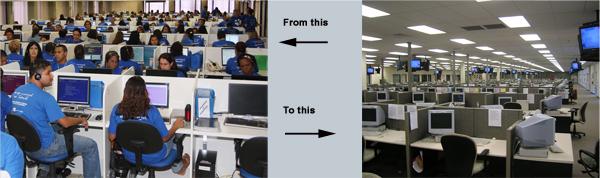

 There are advantages and limitations to each option. Single sign on is probably the best solution, having your users log in once and then be authenticated into each application. However, if the application doesn't support federation, you will need to do password vaulting and you still have the problem of a lot of passwords. Many legacy systems will have this limitation.
There are advantages and limitations to each option. Single sign on is probably the best solution, having your users log in once and then be authenticated into each application. However, if the application doesn't support federation, you will need to do password vaulting and you still have the problem of a lot of passwords. Many legacy systems will have this limitation.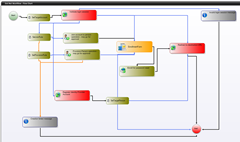 But we haven't really saved IT a lot of time yet unless it's easy to implement and configure. That's where EmpowerID's
But we haven't really saved IT a lot of time yet unless it's easy to implement and configure. That's where EmpowerID's  Even these steps aren't as secure as they could be. Self service password reset rides that delicate balance between productivity and security. Users will forget passwords and get locked out, to minimize the disruption to their work day, you need to offer self service with as few roadblocks as possible. However, the bad guys can take advantage of this lack of roadblocks and reset passwords.
Even these steps aren't as secure as they could be. Self service password reset rides that delicate balance between productivity and security. Users will forget passwords and get locked out, to minimize the disruption to their work day, you need to offer self service with as few roadblocks as possible. However, the bad guys can take advantage of this lack of roadblocks and reset passwords.  As George Orwell said, "All animals are equal but some animals are more equal than others." How does this apply to resetting passwords? Everyone needs passwords reset, but some need a little extra security around their password resetting.
As George Orwell said, "All animals are equal but some animals are more equal than others." How does this apply to resetting passwords? Everyone needs passwords reset, but some need a little extra security around their password resetting.
 As
As 
