The whole goal of authentication is security. There is a lot of buzz around password strength and security, highlighted famously by XKCD. Their theory is that long passwords equals password strength. And it's true, a long password will take a lot longer to crack and if done right is remarkably easy to remember (like your favorite lyric from an obscure polka song).
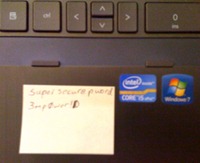 The question is, will users ever take this advice and stop using passw0rd as their password? No. And, even if they do, they will continue to write it on a post-it note affixed to the bottom of their keyboard. This is the inevitable and painful flaw in any password policy.
The question is, will users ever take this advice and stop using passw0rd as their password? No. And, even if they do, they will continue to write it on a post-it note affixed to the bottom of their keyboard. This is the inevitable and painful flaw in any password policy.
You know what solves this? Two factor authentication. Single factor authentication should never be allowed, you need a second factor like the user's phone and/or a hardware token. Something that the user cannot just write down. And that isn't guessable. With a second factor, if someone gets your password, they still cannot access your application or data.
But, come on, are you going to make your users respond to an SMS message or spend the money on an RSA SecurID to check their email or punch in to the timeclock application? Do you want your lowest privileged accounts having to ramp up security that highly?
Enter adaptive authentication. The idea is that the more secure the data and/or application, the higher level of authentication is required. So, your user logs in to the network using just his basic credentials. When accessing email, this is fine. Punching in to the timeclock, this is the appropriate level of authentication.
But, once your user wants to access CRM or Oracle Financials or the SharePoint site with the 10K draft in it, you want adaptive authentication. Your authentication workflow should split out at this higher security application and ask for a second factor authentication.
With this, you are taking a strong password and strengthening it to the nth degree. Your user will need to provide a token or a code from their phone or a fingerprint or their first born, whatever you choose as the second factor. You can even ramp it up and ask for something like Equifax's identity proofing service.
We will never get users to use the appropriately strong passwords we need for security, but using adaptive authentication we can add to password strength with second factor authentication on the most important applications. What the heck, even add a third factor if it's important enough.

 Once confirmed as a problem, what about a solution? There are two ways to go about this, Google Apps password reset or Google Apps single sign-on. It depends on your infrastructure I'm sure and I'm probably looking at this from a very EmpowerID-centric view, but neither is a difficult proposition.
Once confirmed as a problem, what about a solution? There are two ways to go about this, Google Apps password reset or Google Apps single sign-on. It depends on your infrastructure I'm sure and I'm probably looking at this from a very EmpowerID-centric view, but neither is a difficult proposition.
 What you need is
What you need is 

