 We have a very large home healthcare client with a very common problem: most of their employees are on the road needing access to corporate and cloud applications using a tablet. These users have numerous critical applications they need to access for medical history, prescriptions, scheduling and all of the traditional cloud applications. If they couldn't authenticate and log on, they certainly could not call the helpdesk while sitting with their patients.
We have a very large home healthcare client with a very common problem: most of their employees are on the road needing access to corporate and cloud applications using a tablet. These users have numerous critical applications they need to access for medical history, prescriptions, scheduling and all of the traditional cloud applications. If they couldn't authenticate and log on, they certainly could not call the helpdesk while sitting with their patients.
The solution to the problem consisted of three parts:
- Single sign-on using a combination of Federation, Web Access Management (WAM), and password vaulting.
- Role based access control to give the mobile user the correct access within applications.
- Two Factor Authentication using OATH tokens for high security applications.
Single Sign-on to these corporate and cloud applications was the first priority. Because EmpowerID has a metadirectory that inventories and synchronizes identities with all of the applications, we know who the users are. We configured EmpowerID to authenticate the user and present a unified dashboard regardless of the method used for single sign-on. Several of the applications were federated using SAML, Web Access Managent (WAM) was used for most, and one lone legacy app was handled with secure password vaulting.
With a mixture of on-premise and cloud applications, this unified interface is essential for the user experience. EmpowerID's user interface is HTML5 so it configures for the device, giving a modern clean appearance regardless of the screen dimensions (smartphone, tablet, laptop). Device registration adds another layer of security as IT can keep track of the devices used in the field, even limiting access to corporate issued devices in some divisions.
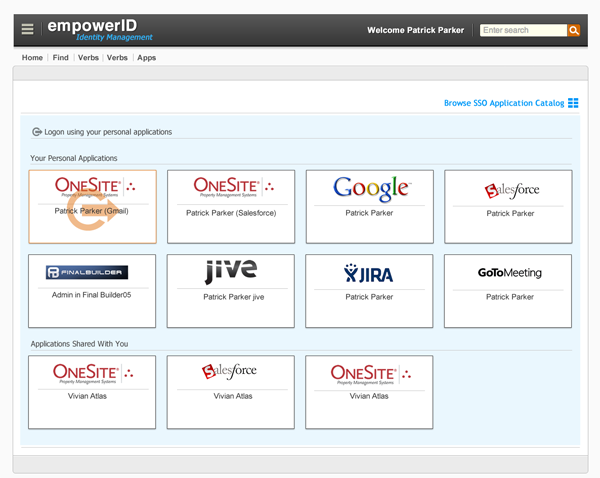
Of course you need to add RBAC to the mix. A nurse doesn't have the same access needs as a doctor or technician or delivery manager. Not only are the SSO dashboards security trimmed based on role(s) but EmpowerID's connectors can project roles into the applications whether they be cloud or on-premise to give the correct access within the application.
These same roles are then used to determine when to demand two factor authentication. Based on a combination of the user's role and the security level of the application being accessed, EmpowerID will demand a second factor using its OATH server. Issuing this OATH token gives a layer of security for both the CISO and the auditors.
Accessing today's complex mix of on-premise and cloud applications from a complex mix of mobile and desktop devices is, in a word, complex. EmpowerID's mix of SSO methods, RBAC workflows and metadirectory simplifies it not only for your users but for IT as well. Schedule a demo and see how Cloud SSO can be made less complex.
Tags: Single Sign-on (SSO)


