Gartner Peer Insights is the market-leading peer-review platform by Gartner for comparing and rating enterprise technology solutions to ease decision-making making journeys for buyers.
We’re incredibly excited to share that EmpowerID ranks among the industry’s leading best-of-suite Identity Governance and Administration (IGA) providers on Gartner's Peer Insights.
More than 50% of our customers have given us a full 5 STAR recommendation on the peer-review website. Let’s see what they have to say about us!![]()
"Simple and Easy to use Identity Management & Cloud Security Platform."
“EmpowerID - One of the Best Application Provisioning Platforms in the Market.”
"We have been able to accomplish more in 6 months with EmpowerID than in 2 years with our previous IAM platform."
“Flexible Pricing and Cost-effective”
“Ahead of its competitors in many things like its Quick Customer Support.”
“I like that it has increased our Workflow Efficiency.”
![]()
Read on Gartner to see what other customers think about EmpowerID's low-code orchestration platform!
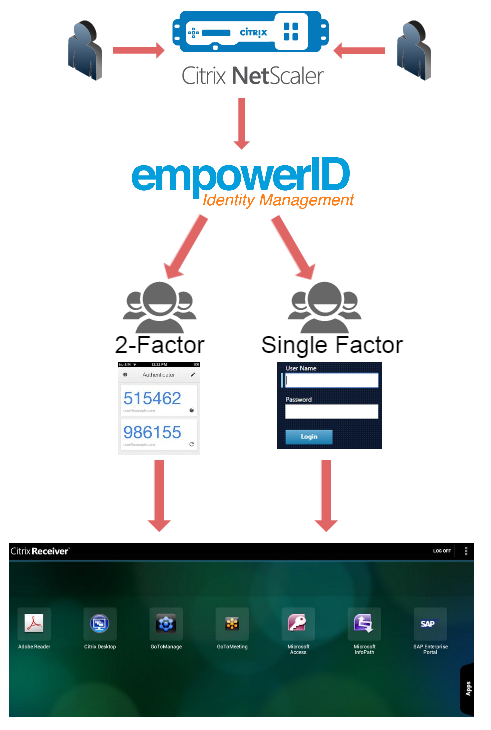
EmpowerID has consistently emphasized our customers' needs in our products. We know that when they succeed with EmpowerID, we succeed. In this past year, as the vast majority of companies shifted towards remote work, EmpowerID was not only their partner to ensure a smooth and secure transition but also a guide in accelerating their digital transformation journey.
Our end-to-end support, starting from the platform itself and extending down the line to the entire Deployment support, is designed to ensure that our customers achieve the fastest time to value and grow their return on investment with EmpowerID right from Day One. Our products, such as Azure License Manager and Azure SCIM VDS, reflect all these ideals.
Identity Governance and Administration (IGA)
In Gartner’s Words, IGA or Identity Governance and Administration refers to managing “Access rights for Individuals, Roles, Groups, and identity repositories within organizations, both on-premises and in the cloud. Ensuring appropriate access to resources across highly connected IT environments.”
For an IGA platform, it is necessary to have a broad array of capabilities in order to meet the needs of the ever-growing complexities of modern organizations and IT Systems, these features that complete an IGA Suite are: Identity life cycle management, Entitlement management, Support for access requests; Workflow orchestration; Access certification Provisioning via automated connectors and service tickets; Analytics and reporting.
In 2020, Gartner chose to retire it’s incredibly viral Magic Quadrant for IGA. This was because the Magic Quadrant is designed to capture the most significant innovations in a particular market, but since IGA has already had it’s exponential growth phase, and has reached a state of maturity, it has made measuring improvements much more, but that doesn’t mean that growth has stopped. With the shifting of existing work models in the post-COVID world, IGA has seen growth and expansion to previously unimaginable heights.
IGA today has expanded and adapted to manage increasingly complex Identities spanning across different cloud platforms to provision access and entitlement of the vast repertoire of applications that modern enterprises use today in their ever-expanding workflows.
You can learn more about how EmpowerID competes in these ever-expanding domains in this all-new 2022 Leadership Compass Report by Kuppinger Cole, which examines the market for solutions that increase security in business application environments for managing cloud entitlements—measuring the growth of IGA and Access Management platforms beyond the traditional limit of imagination, taking a much more abstract and out-of-the-box approach to evaluate the needs of modern enterprises.
Check it out in the link below.



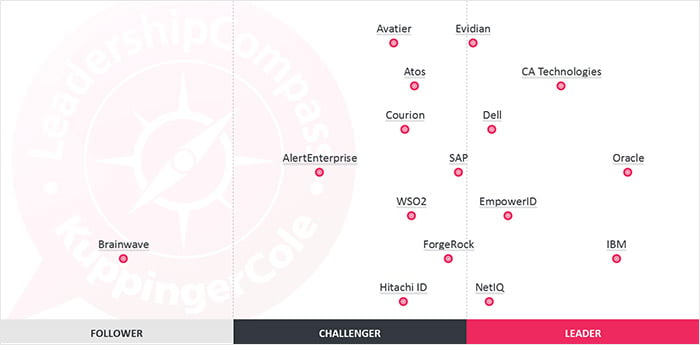
 KuppingerCole, a respected global analyst focused on Information Security, examined 24 vendors in the Identity as a Service, Business to Enterprise market (IDaaS B2E) market. EmpowerID was named as a Product Leader, a category which ranks vendors by functional strength and completeness of solution. KuppingerCole stated in the report that EmpowerID "delivers a very broad feature set for Identity and Access Management, going well beyond Identity Provisioning but with tight integration to these core features."
KuppingerCole, a respected global analyst focused on Information Security, examined 24 vendors in the Identity as a Service, Business to Enterprise market (IDaaS B2E) market. EmpowerID was named as a Product Leader, a category which ranks vendors by functional strength and completeness of solution. KuppingerCole stated in the report that EmpowerID "delivers a very broad feature set for Identity and Access Management, going well beyond Identity Provisioning but with tight integration to these core features."